Every modern application team today faces the same paradox: Kubernetes gives us unmatched agility, but it also makes visibility and compliance dramatically harder. With ephemeral pods, shifting network paths, and dynamic workload changes, proving what your system looked like at any point in time becomes almost impossible with traditional logging or metric-only tools.
Now imagine you had a system that not only watched every part of your cluster continuously, from nodes and workloads to network paths and policy changes, but also stored that information in a queryable history from the moment you first activated it. Over time, you build up a rich timeline of your cluster’s structural state, not just performance metrics.
That system is CloudInspector.
But why does this matter? Especially for organisations that must meet strict compliance frameworks like the German BSI’s Cloud Computing Compliance Criteria Catalogue (C5), official documentation and international standards such as ISO/IEC 27001:2022 are important.
Let’s dive in.
Why Traditional Observability Isn’t Enough
Most monitoring stacks focus on:
- metrics (CPU, memory, latency),
- logs of discrete events,
- and some traces for application behaviour.
But cluster structure, the concrete, evolving system topology and component relationships, is not something these tools preserve over time. In Kubernetes, the cluster topology literally changes by design: pods die and spin up, network rules evolve, and RBAC bindings shift with deployments.
As a result:
- You can struggle to demonstrate which workloads were running in which namespace at a given audit cut-off.
- You often can’t show what network connections existed between services when an incident occurred.
- You have few reliable artefacts to prove policy states to auditors because most observability tools don’t store cluster metadata historically.
- Yet auditors and compliance frameworks demand this kind of insight: not snapshots, but evidence of what the infrastructure actually looked like at specific times.
C5 and ISO 27001: What They Require — and Why Structure Matters
The C5 Cloud Computing Compliance Criteria Catalogue is a security baseline developed by the German Federal Office for Information Security (BSI). It lays out minimum requirements for cloud security controls, particularly for providers and users of cloud services that must satisfy German public-sector or regulated-industry expectations. The goal of C5 is to ensure transparent, auditable evidence of control implementation in cloud environments, not just claims.
On the other hand, ISO/IEC 27001:2022 is an internationally recognised standard for Information Security Management Systems (ISMS). It defines how an organisation must establish, implement, maintain, and continually improve a formal system for managing risk and securing information assets.
Both frameworks share a deep emphasis on documentation, traceability and evidence of controls:
- ISO 27001 requires organisations to demonstrate risk assessment processes, control implementation, monitoring, review, and continuous improvement.
- C5 requires demonstrable cloud-specific controls and evidence of those controls being alive and enforced over time.
What C5 and ISO 27001 do not accept is a vague or ad-hoc approach. They expect organisations to show who did what, when, and how the system reacted or changed.
Enter CloudInspector: The Compliance-Sensitive View of Your Cluster
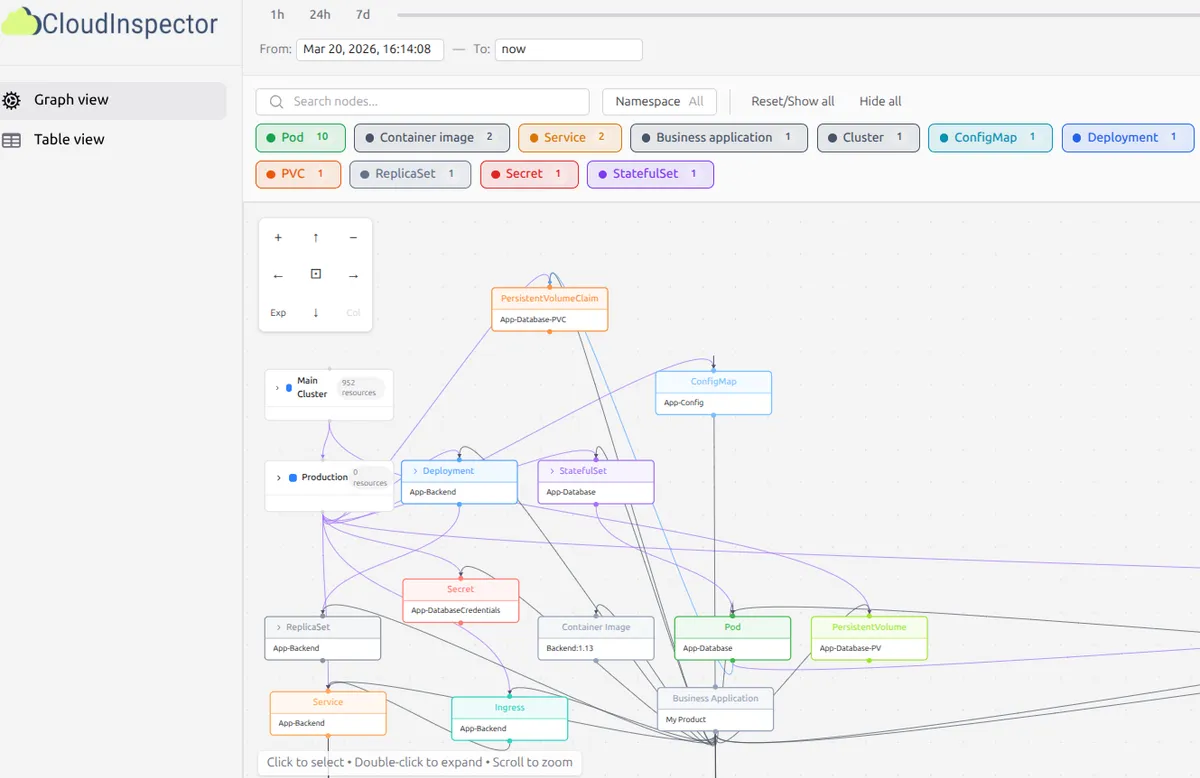
CloudInspector addresses a fundamental gap: the lack of continuous, historical understanding of your cluster’s structure and relationships.
From the moment it starts, CloudInspector:
- Actively and constantly collects structural metadata from your cluster: workloads, pods, namespaces, services, RBAC settings, network policies, and the relationships between them.
- Stores this data in a purpose-built database, preserving a timeline of configuration and topology.
- Allows you to visualise and query historical states, in other words “time-traveling” to see exactly how your cluster looked at any moment in the past.
Offers interactive visual representations and reports that can stand up to audit scrutiny.
That means:
- You can show compliance auditors exact states — not approximations — of deployments, network allowances, and access paths on specific audit dates.
- You can identify when a security policy drifted or when control enforcement changed.
- You can reconstruct the evidence trail for a security incident — including dependencies, connections, and exposures over time — even if the original workloads have long since disappeared.
This goes far beyond metrics or logs. Those tools tell you what happened, CloudInspector tells you what the system looked like and why.
Why Historical Structural Insight Matters for Compliance
Both C5 and ISO 27001 share a core theme: visibility equals accountability.
Under C5, cloud controls must be proven, and cloud security evidence must be transparent over time. It is not enough to say “we enforce network policies”; you must show which policies were in effect historically and how they were enforced.
ISO 27001 requires organisations to demonstrate an ongoing risk-based approach to security, supported by documented evidence of control effectiveness. Metrics alone don’t suffice: you need traceable records showing system configuration and change management over time.
CloudInspector bridges the conceptual gap between “monitoring” and “audit evidence.” It preserves structural metadata that auditors can query directly, supports compliance reporting, and helps answer questions like:
- Which services were communicating with each other on June 10 last year?
- What network segmentation existed on a specific audit snapshot?
- Who had access to what — and when that access was modified?
This level of traceability is exactly what C5 attestations and ISO 27001 audits expect.
Turning Compliance From a Burden Into a Competitive Advantage
Many teams treat compliance as a hurdle, like a periodic audit that causes pain. But compliance frameworks like C5 and ISO 27001 are ultimately about building confidence in your ability to manage risk and evidence control effectiveness.
With CloudInspector:
You move from reactive “audit preparation” to proactive evidence readiness.
You gain insight that is useful for both DevOps teams day-to-day and security and compliance teams during audit cycles.
You reduce friction between security controls and compliance demonstrations.
In a world where infrastructure is fluid but regulatory expectations are fixed or becoming stricter, having continuous structural intelligence is not just valuable, it can be a differentiator.
Make your first step towards compliance with CloudInspector now!